The Surveillance Society Is Here, and What You Can Do to Protect Yourself
George Orwell’s 1984 featured a dystopian England, and indeed, a world, of three superstates that all ran according to the same principles. Eternal war, eternal ignorance, and eternal subservience, whether realized or not. BIG BROTHER IS WATCHING YOU was this book’s addition to the American lexicon for many, many people.
The means of surveillance were certainly in keeping with the author’s current knowledge of technology, for the television had just been developed, through wireless radio and microphone / recording systems were well developed. It was easy for Orwell in 1948 to envision a surveillance society based on the media of his time, alone.
What he did not bet on was that it would not take an expressly socialist government, nor even a Communist one to create this sort of surveillance state.
How about using social media instead? How about using the apps that are mainly toys for the smartphone user? How about using a globally popular platform and asking for the permissions to be surveilled in plain sight, and in plain English?
Couldn’t possibly be true, could it? We are a free people, and the right to privacy is ours, isn’t it?
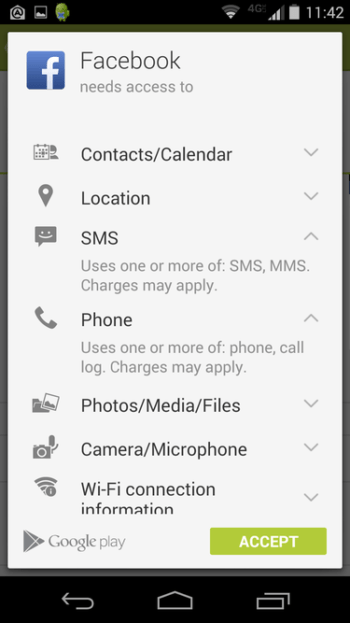
Sure it is. But have you ever seen these before?
These are the permissions screens for Google Play when one installs a new app on their Android device. If you read carefully, you can see that these apps are asking for access to various functions on your phone. But think:
- Does it make sense for Spotify to have access to your Device ID, and your phone call information?
- Does it make sense for Move to iOS to have access to your Short Messages (SMS) – I mean the texts that reside on your phone, itself?
- Does it make sense for Facebook to have access to your contacts?
- And the information about the permission READ_PHONE_STATE: Look at the details. Did you know that some apps can do what this says – to access the phone features on your device, to determine phone number and device ID and to know who you are calling when you call them?
“I have a funny feeling that I am being watched.”
It looks like this saying has a lot of truth behind it in our smartphone and device-filled world. While some permissions listed here DO make sense, there are rather significant questions about others.
Usually we do not consider these permission screens when we download an app, because we want to play the game or listen to the music. Google Play offers an astounding array of services for no monetary cost, but they do get something out of the transaction. Information. Personal information. And we have seen and heard evidence that this ability to silently monitor what we do gives companies, individuals and maybe even governments – the ability to watch and listen, and maybe even influence our actions.
One story was that someone was in a meeting with friends, talking about travel destinations, and the person talked a lot about interest in visiting Thailand. They did not remember ever using their device to investigate the possibility of going there, but within a couple days of the conversation, a message popped up on their device with a travel offer to Thailand. Coincidence? Maybe.
Or, maybe not. A similar story was reported by an Instagram user, shown at this link.
According to Andrey Meshkov, CTO and Founder of AdGuard, in his blog piece here, many apps available through Google Play have very poor compliance with what is also itself a very poorly defined security and privacy structure that is presently characteristic of Android. (iOS is far better on privacy matters currently, due to comparatively limited capabilities within iOS – Android is far more sophisticated)
Now, to be sure, in legalese, Google does insist that privacy and security requirements exist and are strict, and on their page they specifically do say what apps are not allowed to do:
Your in-app disclosure:
- Must be within the app itself, not only in the Play listing or a website;
- Must be displayed in the normal usage of the app and not require the user to navigate into a menu or settings;
- Must describe the type of data being collected;
- Must explain how the data will be used;
- Cannot only be placed in a privacy policy or terms of service; and
- Cannot be included with other disclosures unrelated to personal or sensitive data collection.
Your app’s request for consent:
- Must present the consent dialog in a clear and unambiguous way;
- Must require affirmative user action (e.g. tap to accept, tick a check-box, a verbal command, etc.) in order to accept;
- Must not begin personal or sensitive data collection prior to obtaining affirmative consent;
- Must not consider navigation away from the disclosure (including tapping away or pressing the back or home button) as consent; and
- Must not utilize auto-dismissing or expiring messages.
However, there is a great deal of evidence to suggest that this is not well-enforced, and that in fact, a great deal of personal information collection does take place, including actual SMS messages, phone call records, photo and video collecting, even audio recording, as well as IMSI, and IMEI information, and device location.
A deeper look at IMSI and IMEI – what are these?
The IMSI and IMEI are of great importance because these numbers are unique identifiers. The IMSI (International Mobile Subscriber Identity) is the unique identification of every SIM card in existence. It is generally 15 digits long, and contains two prefix headers and a subscriber ID. It looks like this:
For an AT&T Subscriber,
IMSI: 310150123456789
MCC (Mobile Country Code) 310 USA
MNC (Mobile Network Code) 150 AT&T Mobility
MSIN (Mobile Subscription Identifcation Number) 123456789
This differs from the MSISDN, which is what we commonly refer to as the Phone Number. MSISDN’s can be changed easily, and in fact this is offered as a service to end-users by any and all cellular carriers. But IMSI numbers are unique and difficult to change without access to the core network of a given cellular provider.
The IMEI is the International Mobile Equipment Identity, and this number is unique to the phone or device itself. It is also possible to change, but special tools are required, and it is designed with the intent to not be changed.
Together the IMSI and IMEI equal… you! As cell and satellite networks constantly track any mobile device with these numbers, this means that unless you are in a place with no cell or satellite coverage, you are being tracked. And that little “location” tag in the permissions can be exploited by anyone who wants to read that information. The fact that the cell network keeps track of your location is basically good, especially if you are in an emergency. However, badly or maliciously written apps can take advantage of this in very unwanted ways.
Adguard conducted a test. They devised a test app for Android that basically didn’t do anything. However, that app was easily able to silently acquire:
- Email addresses
- IMEI
- All your contacts
- All your SMS messages
- and the app was capable of gathering more information if programmed to do so.
And, it could send all that data wherever desired.
Andrey Meshkov admits that this is not necessarily or constantly used for illegal or hostile intent. But he does point out that both Google Play and Android privacy protections are extremely poorly handled, and this could lead to unsavory folks getting access to your personal life, including text messages and knowledge of who you call.
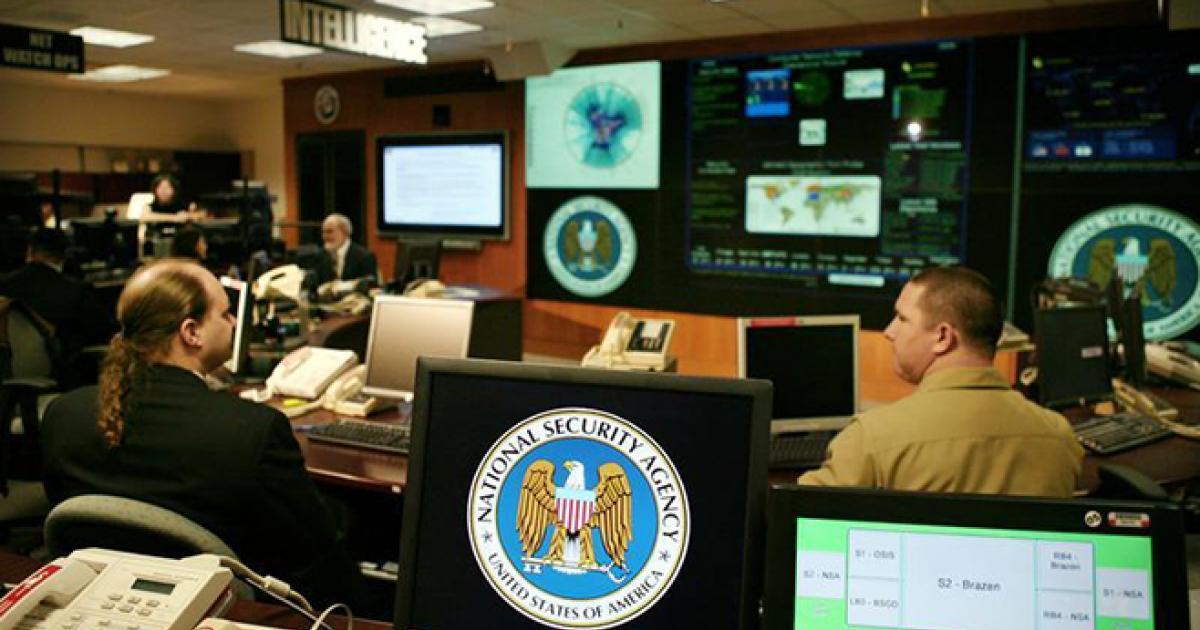
This incidentally provides some background into the American investigation into the alleged collusion of Russian agencies with the Trump campaign. While no evidence of such collusion exists, there have been quite astounding revelations about the internal collusion of the FBI and other intelligence agencies and “deep state” activity within the American Federal government, all purposed to take down Donald Trump or block him at every turn.
The recent news pieces regarding the 50,000 text messages sent between two romantically involved FBI agents that probably denigrated Trump in their pillow talk are examples of this sort of technology being used to track and observe what people say and do and think.
Meshkov advises anyone wanting to preserve their privacy to do these actions:
- Do not install apps from developers you don’t trust.
- Examine the apps’ permissions very carefully. After all, why would a wallpaper app or a selfies editor need to get access to your accounts information?
And of course, their own product, Adguard offers some control over this activity. While this is not an advertisement for their company, discovering and dealing with these situations is what they do. So, they further advise that if you are one of their users, use their filtering log to examine the apps’ network activity.
It is very interesting when Life imitates Art.
By Seraphim Hanisch
Source: The Duran